The New Paradigm for Accessing IT Resources
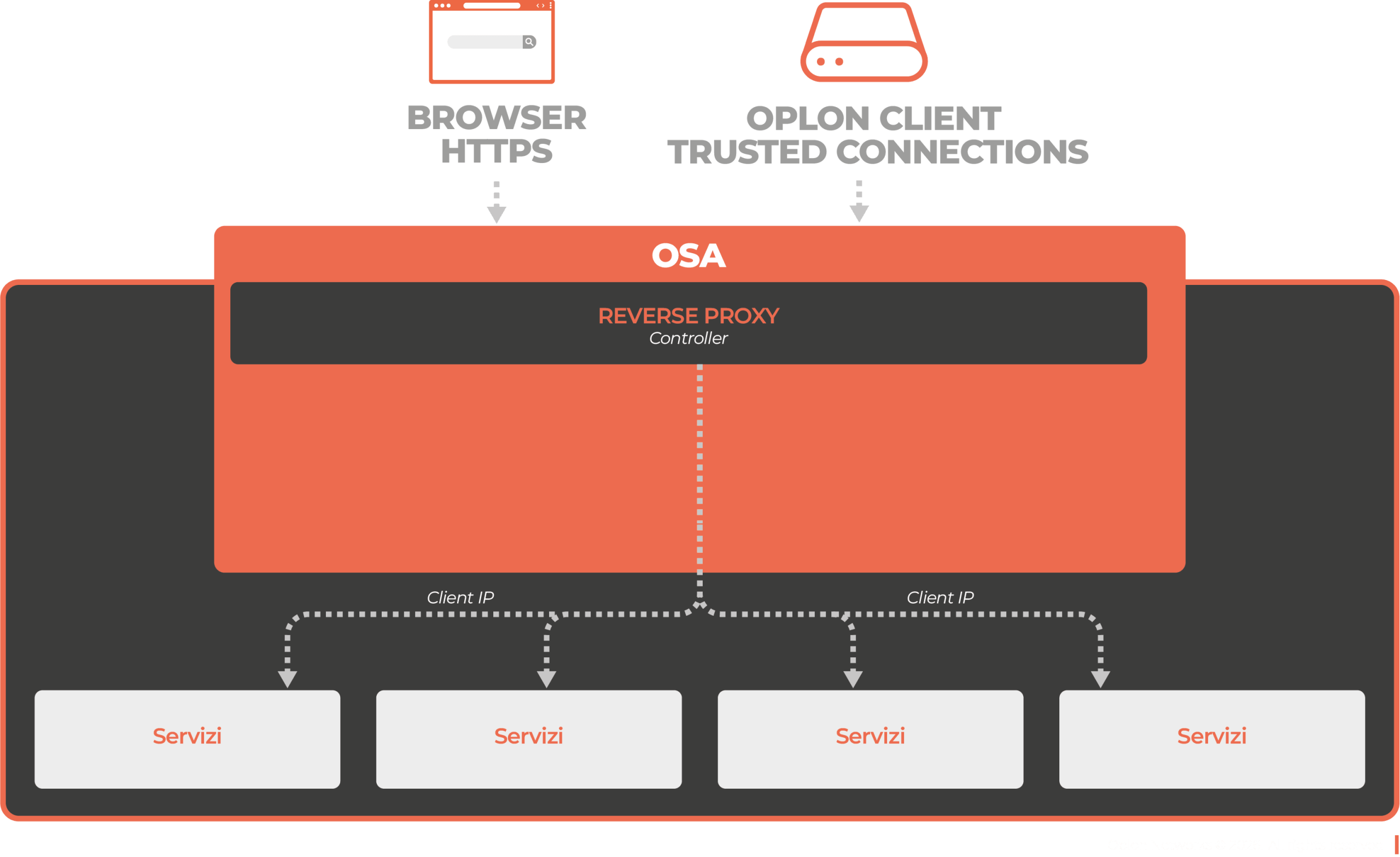
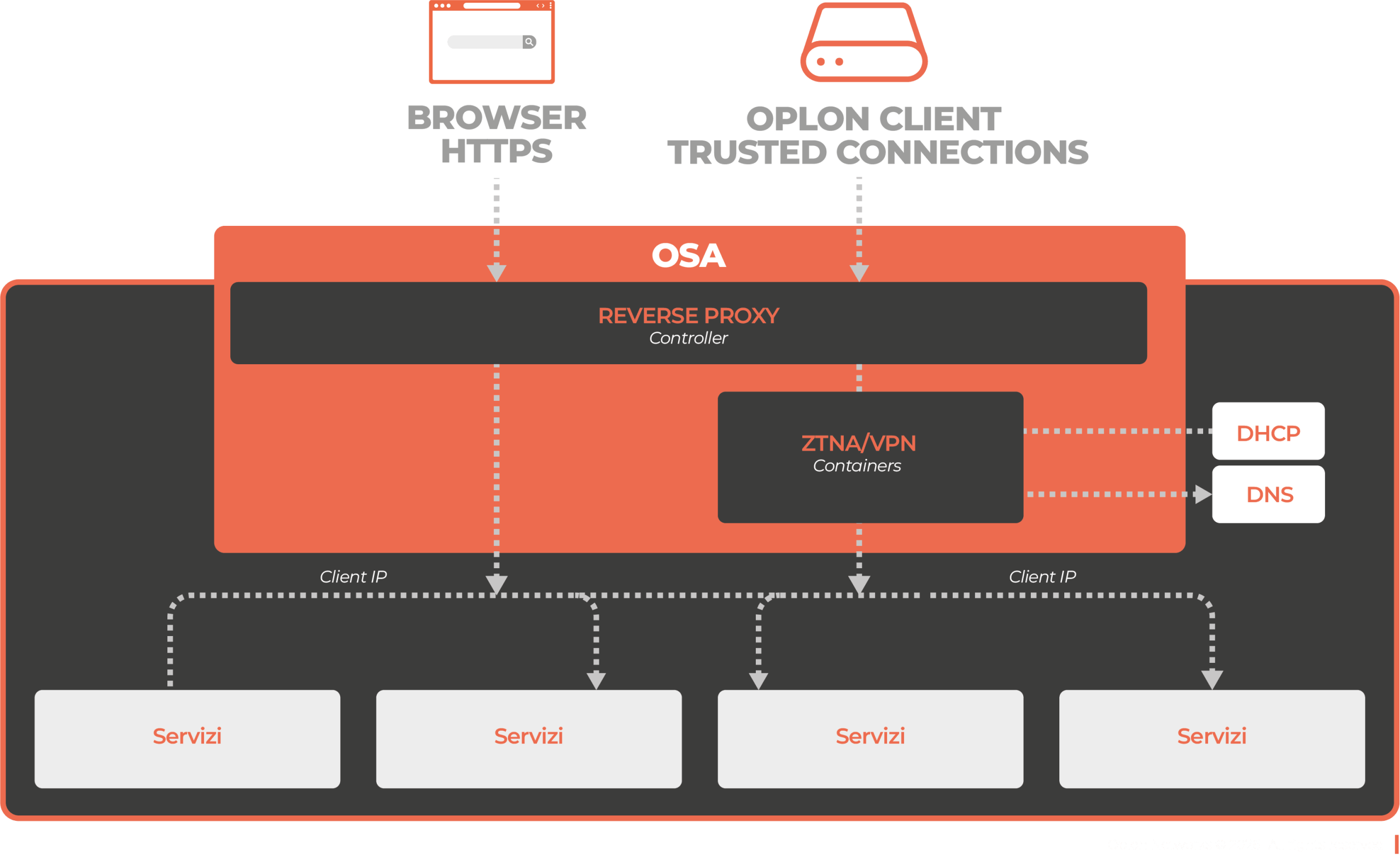
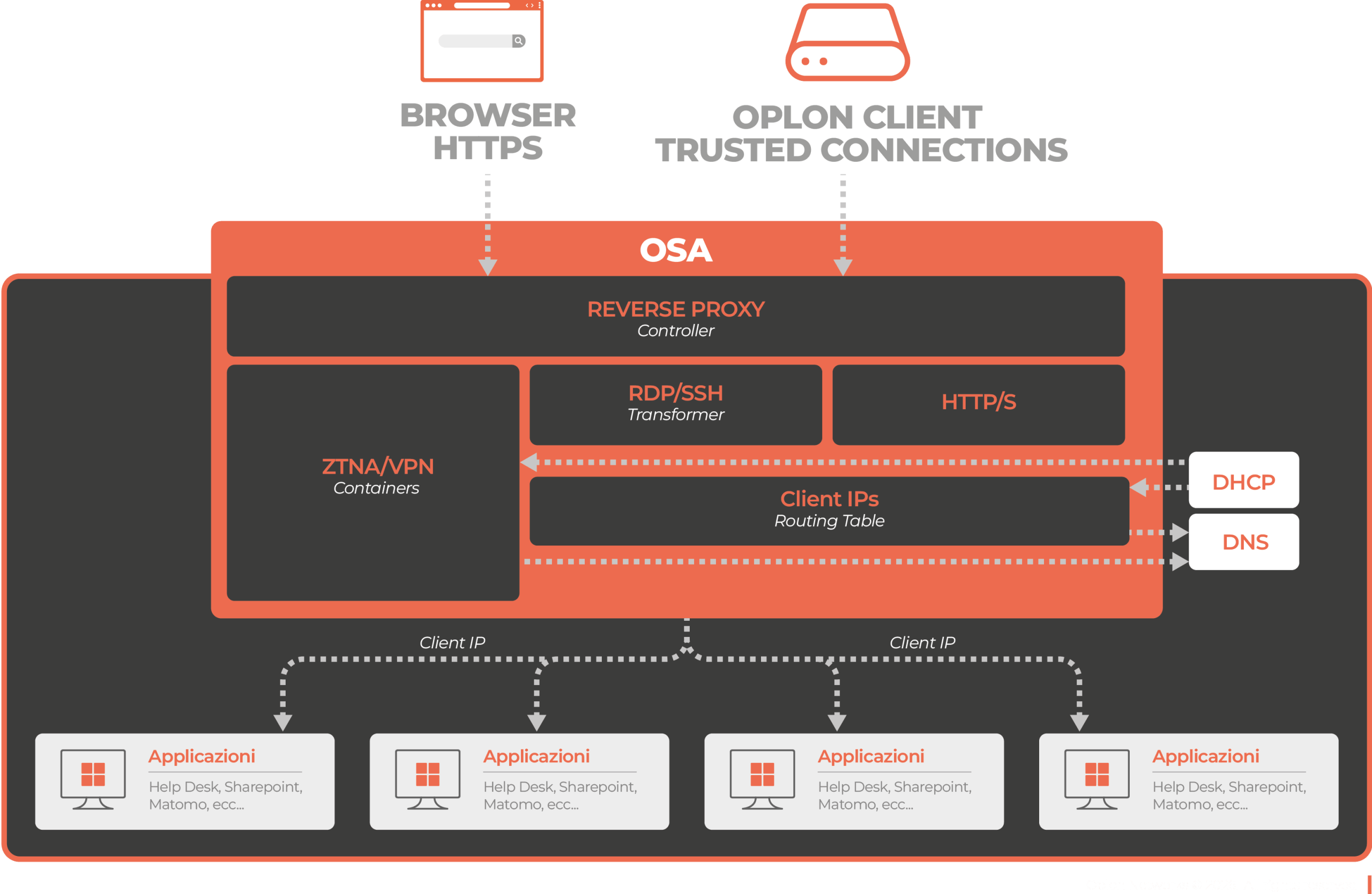
Oplon Trusted Connections introduces a new approach to enterprise connectivity: connecting people to resources, not to networks. By integrating modern security with existing infrastructure, it enables secure HTTPS access without exposing the entire network, overcoming the limitations of traditional VPNs. Thanks to an intelligent application layer and the use of isolated containers, it provides granular control, compatibility with legacy systems, and integration with corporate DHCP and DNS. The result is a hybrid model that combines Zero Trust with classic networking, improving security, visibility, and management without disrupting existing operations.