Oplon Secure Access is out.
Traditional security models rely on network boundaries. Modern organizations are distributed. You need to control who accesses what, and under which conditions.
Oplon Secure Access centralizes authentication, authorization, and connection to corporate resources, applying a Zero Trust model: every access is verified, restricted, and monitored.
Privileged sessions are isolated, monitored and fully auditable, reducing the risk associated with high-level permissions.
Oplon centralizes authentication and authorization across the organization, enforcing consistent access policies based on identity and context.
It integrates with existing identity providers and acts as a control layer for all access requests.
All access requests are evaluated by a single control point, ensuring consistent enforcement of authentication and authorization rules across systems and applications.
Oplon integrates with existing identity providers, allowing organizations to leverage their current user directories while maintaining unified access control.
Access rules are defined once and applied uniformly to all protected resources, reducing configuration errors and policy fragmentation.
All access requests are evaluated by a single control point, ensuring consistent enforcement of authentication and authorization rules across systems and applications.
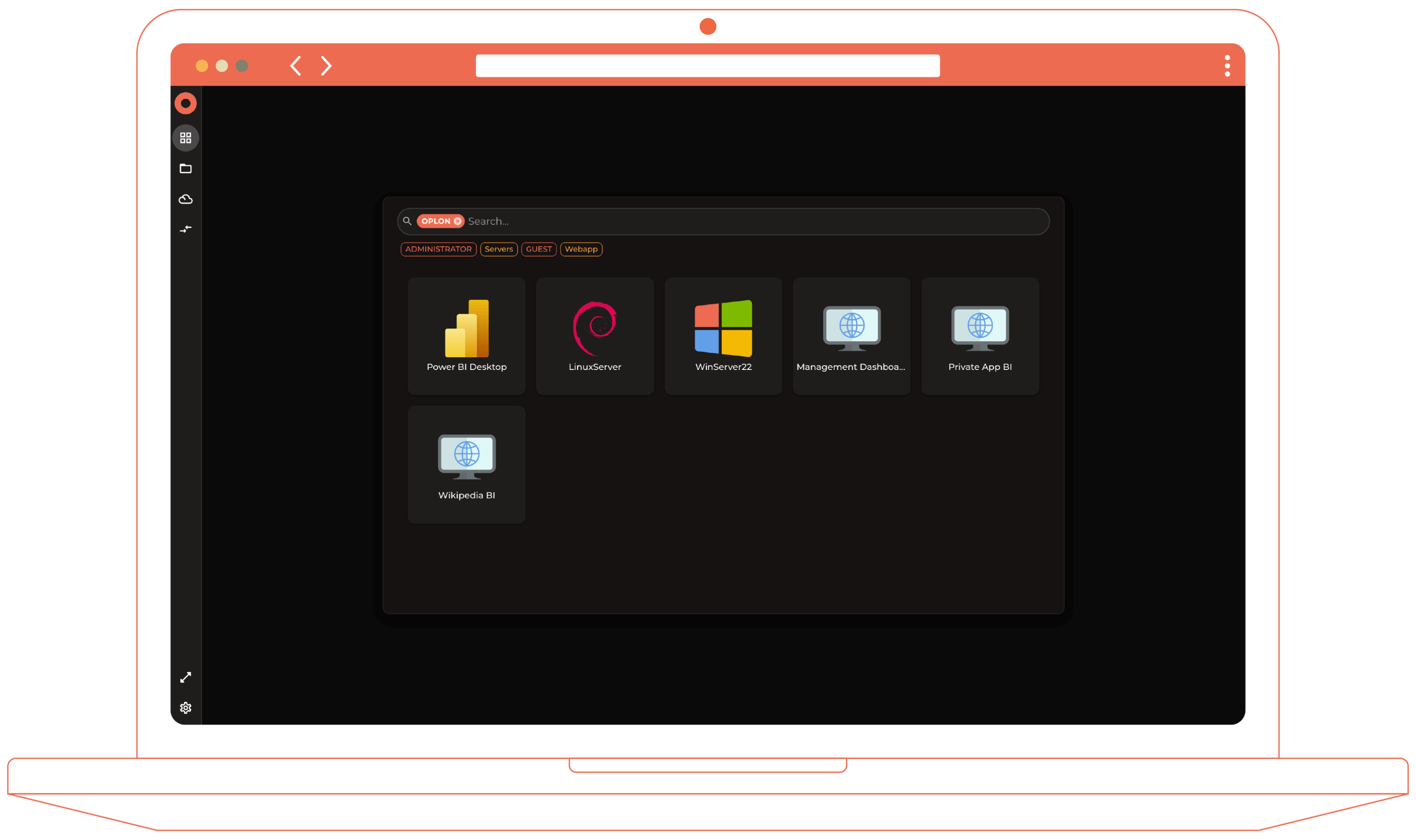
Oplon Secure Access provides a single, centralized interface for accessing protected resources.
The same interface is used by different user profiles, ensuring a consistent and controlled access experience across the organization.
Oplon Secure Access provides multiple access methods to securely connect users to applications and systems without exposing the network.
These methods support common use cases such as remote access, third-party connectivity and legacy application protection.

Key capabilities
Benefits

Key capabilities
Benefits

Benefits

Benefits

Multi-factor authentication without changing the app
Benefits
Oplon Secure Access combines policy-based control with practical access tools that allow users to connect to authorized resources in a consistent and governed manner.
Oplon Secure Access supports access control requirements across different operational contexts, enabling secure connectivity to systems and applications without relying on broad network exposure





Discover how Oplon Secure Access can strengthen identity protection and improve your organization’s security posture.
Get in touch with our team to request a demo or schedule a conversation with one of our specialists.